Backup data, and backup monitoring, is regularly thought of as the last line of defense in the case of cybersecurity threats. It ensures that critical data is available and restorable in the event of a successful ransomware or malware attack.
While this is certainly one role of backup monitoring, on its own it’s an extremely reactive approach. In fact, backup monitoring can be a proactive way of getting ahead of cybersecurity issues. By keeping a regular eye on variances in bytes being backed up, a practice that can be easily streamlined through automated backup monitoring software, IT administrators can play an active role in cybersecurity defense.
How Ransomware & Malware Impact Backup Byte Count
There are a variety of ways in which cybersecurity threats manifest by changing backup data byte counts:
- Ransomware Removes Files: Perhaps the most common cybersecurity scenario that impacts byte count is ransomware completely removing files. This will immediately result in files now appearing as having no backup volume whatsoever. Because ransomware can remove just a few files at a time, the process can go on for quite some time, and impact a large number of critical files unless it’s spotted early.
- Ransomware File Replication Alters Files: A related ransomware practice is the changing of a file name or extension. The malware then replicates the file and gives this new file the original file’s name. At the same time, it might delete the original “good” file all while altering the contents of the new “bad” file. This can be almost undetectable, yet the byte count decrease or increase that may result is an indicator of this behavior.
- Malware Encryption Changes File Size: Another malware practice is the encryption of files on your servers. This leaves files unable to be accessed unless the encryption key is made available, usually for a price. An unusual outcome of this encryption can be a significant increase in file size. In fact, files that are base64 encoded can grow as much as 35% in byte size. Byte count growth detection can help you get ahead of this encryption hitting a wide range of critical files.
- Embedded Malware Is Extremely Large: While less common, Kaspersky Labs has reported that malware inserted into files is sometimes as large as 100MB. Because many anti-virus programs focus on detecting small, unexpected files, malware producers sometimes include junk data in the malware file to artificially increase its size and avoid detection. However, with unusual byte count growth identification in place, IT teams can get ahead of this.
How Bocada Proactively Identifies Byte Count Variances
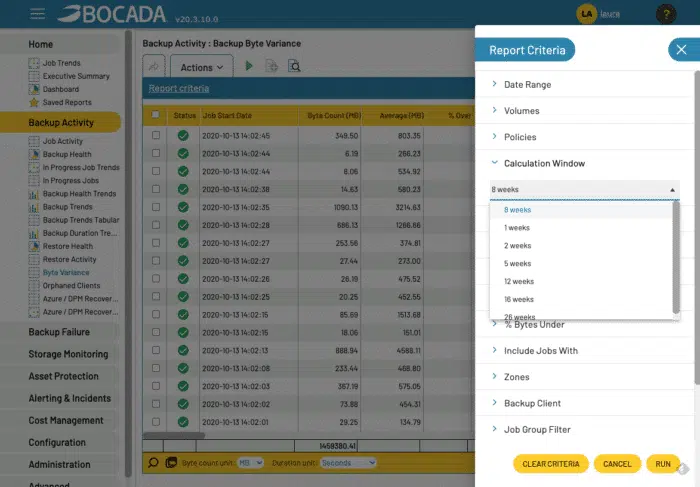
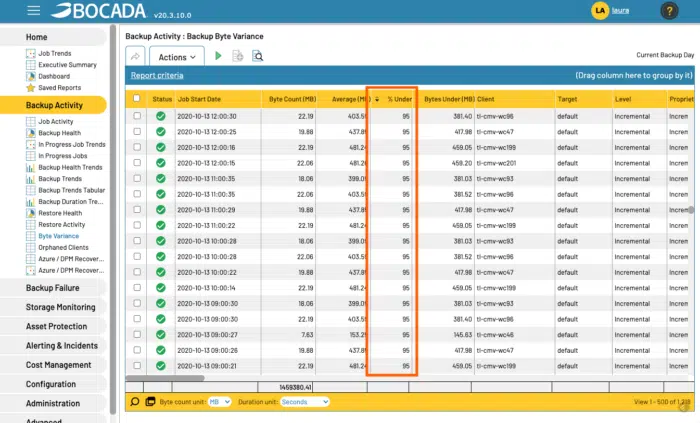
One of Bocada’s many built-in reports is the Bytes Variance Report, designed to identify unusual backup byte activity. The report acts by first assessing historical norms in bytes backed-up based on a user-specific span of time. It then lets users select how they want to see unusual variances, either by changes in absolute bytes or by a % of bytes under or over a certain threshold.
The report lets you sort jobs based on the bytes threshold of interest. In the case below, we’ve sorted it by an unusually small bytes volume being backed up on a percent basis.
By offering an automated process for pinpointing jobs that may have succeeded but have unusual changes in byte volume, admins now have a proactive tool for identifying potential cybersecurity issues and putting stronger safeguards into their backup environments.
For a dynamic tour of the Bytes Variance report and how it can help you get ahead of cybersecurity issues, watch the video below: