Table of Contents
- What is NIS2?
- What organizations will be required to comply with NIS2 (and associated legislation from member states)?
- What are some of the measures that will be required by NIS2?
- What does NIS2 mean for data protection professionals?
- What is the difference in NIS2 enforcement between “essential” and “important” entities?
- What are the consequences of non-compliance?
- When does NIS2 go into effect?
What is NIS2?
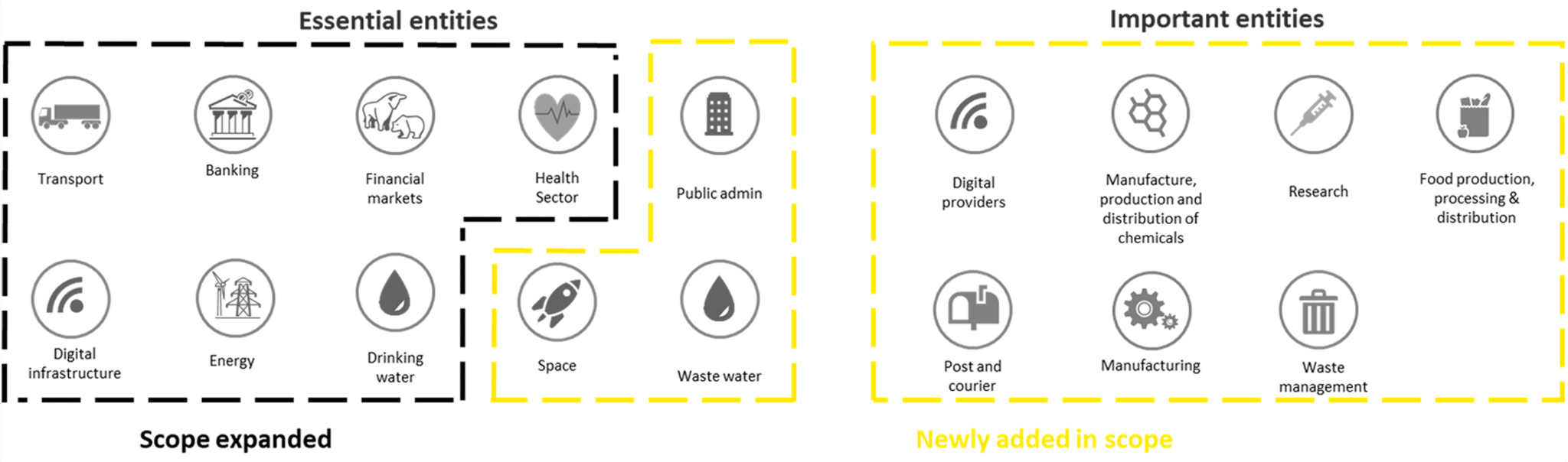
NIS2 (Directive (EU) 2022/2055 of the European Parliament and the Council) is a new cybersecurity directive that greatly expands the scope of previous EU cybersecurity legislation (NIS in 2016) to include “essential” and “important” entities across many more industry sectors, while establishing an even higher standard for cybersecurity and resilience.
Note: Please refer to the full English-version text here.
What organizations will be required to comply with NIS2 (and associated legislation from member states)?
While each EU member state will be responsible for creating and managing its own lists of essential and important entities, here are some guidelines to give an initial idea of NIS2’s scope:
- NIS2 applies to any organization that provides essential/important services within the EU.
- NIS2 covers medium-sized (between 50 and 250 employees) and large-sized organizations (more than 250 employees OR annual turnover of at least 50 million euros OR a balance sheet total of at least 43 million euros).
- The sectors that NIS2 will regulate will be classified as either “very critical” or “critical”, and this (in combination with organization size and other factors) will determine whether an entity is “essential” or “important” for the purposes of enforcement.
NIS2 Sector Classifications:
Note: Qualified trust service providers, domain name registries, and DNS service providers are considered “essential”, regardless of their size.
More information on how “essential” and “important” entities will be determined can be found in Article 3(1) in the full text.
What are some of the measures that will be required by NIS2?
Adequate risk management measures “based on an all-hazards approach that aims to protect network and information systems and the physical environment of those systems from incidents, [shall] include at least the following:”
(a) policies on risk analysis and information system security;
(b) incident handling;
(c) business continuity, such as backup management and disaster recovery, and crisis management;
(d) supply chain security, including security-related aspects concerning the relationships between each entity and its direct suppliers or service providers;
(e) security in network and information systems acquisition, development and maintenance, including vulnerability handling and disclosure;
(f) policies and procedures to assess the effectiveness of cybersecurity risk-management measures;
(g) basic cyber hygiene practices and cybersecurity training;
(h) policies and procedures regarding the use of cryptography and, where appropriate, encryption;
(i) human resources security, access control policies and asset management;
(j) the use of multi-factor authentication or continuous authentication solutions, secured voice, video and text communications and secured emergency communication systems within the entity, where appropriate.
(Source: Article 21 of the NIS2 Directive.)
What does NIS2 mean for data protection professionals?
While the directive ostensibly focuses on cybersecurity, it also very explicitly describes the need for data protection practices in item “C” of the list above:
“(c) business continuity, such as backup management and disaster recovery, and crisis management; “
This is a clear acknowledgment that incident prevention (through cybersecurity) isn’t enough. When incidents inevitably occur (regardless of the cause), organizations must be able to maintain business continuity by recovering quickly.
For data protection professionals, there are two basic implications:
- Your critical data must be adequately protected by backup and disaster recovery operations.
- You must be able to demonstrate that the necessary backup/DR policies are in place to meet target RTOs (recovery time objectives), RPOs (recovery point objectives), and other KPI.
Note: While the vast majority of organizations have data protection solutions in place, many lack monitoring and reporting tools that can easily demonstrate efficacy and compliance.
What is the difference in NIS2 enforcement between “essential” and “important” entities?
The main difference is that essential entities will be subjected to proactive monitoring/auditing. That is, even when there has not been a cybersecurity incident, essential entities will be required to demonstrate that they are following compliant measures. This may occur in the following forms:
(a) on-site inspections and off-site supervision, including random checks conducted by trained professionals;
(b) regular and targeted security audits carried out by an independent body or a competent authority;
(c) ad hoc audits, including where justified on the ground of a significant incident or an infringement of this Directive by the essential entity;
(d) security scans based on objective, non-discriminatory, fair and transparent risk assessment criteria, where necessary with the cooperation of the entity concerned;
(e) requests for information necessary to assess the cybersecurity risk-management measures adopted by the entity concerned, including documented cybersecurity policies, as well as compliance with the obligation to submit information to the competent authorities pursuant to Article 27;
(f) requests to access data, documents and information necessary to carry out their supervisory tasks;
(g) requests for evidence of implementation of cybersecurity policies, such as the results of security audits carried out by a qualified auditor and the respective underlying evidence.
For data protection and backup professionals, backup performance audits and related backup reporting could be included in these “random checks”, “regular and targeted security audits”, “ad hoc audits”, and/or other requests for information. Therefore, it will likely be critical for essential entities to have comprehensive backup monitoring and reporting capabilities in place before enforcement begins.
Important entities, on the other hand, will have reactive reporting requirements. After an incident, the entity will face enforcement scrutiny and can be subjected to penalties if it is determined that the necessary measures were not in place (prior to an incident). It is important to note that important entities must still follow the same risk management measures as the essential entities.
What are the consequences of non-compliance?
Firstly, NIS2 allows for a number of sanctions against infringing organizations, including public warnings, binding instructions to make changes, temporary suspensions of services and/or personnel, and more.
Further, NIS2 sets forth the possibility of administrative fines levied by individual member states, as follows:
- Essential Entities: a maximum of at least EUR 10 000 000 or of a maximum of at least 2 % of the total worldwide annual turnover in the preceding financial year of the undertaking to which the essential entity belongs, whichever is higher.
- Important Entities: a maximum of at least EUR 7 000 000 or of a maximum of at least 1,4 % of the total worldwide annual turnover in the preceding financial year of the undertaking to which the important entity belongs, whichever is higher.
See Chapter VII for more details about supervision, enforcement, and penalties.
When does NIS2 go into effect?
By 17 October 2024, EU member states must integrate NIS2 provisions into their own local legislation.
Important: Many organizations that will be considered either “essential” or “important” are taking steps now to ensure they adopt the necessary cybersecurity and data protection measures ahead of time.
If you are a data protection or backup & storage professional and you anticipate challenges proving NIS2 compliant backup and disaster recovery operations, please get in touch with Bocada for a free consultation.