Going to the cloud for data protection isn’t a matter of if, but when. The speed, flexibility, and best-in-class technology afforded by cloud-based solutions makes this transition inevitable. However, these digital transformations do not do away with age-old data protection challenges like being certain that data and critical resources are fully protected. In fact, these transformations can add greater environment complexity making data protection confidence that much harder.
See how automated protocols overcome many of these challenges, allowing organizations to reap the benefits of cloud infrastructures while continuing to safeguard key resources.
Gain Confidence Over Policy Configuration
Establishing and setting backup policy parameters is at the core of any well-running, compliant data protection operation. This certainly does not change with cloud migrations.
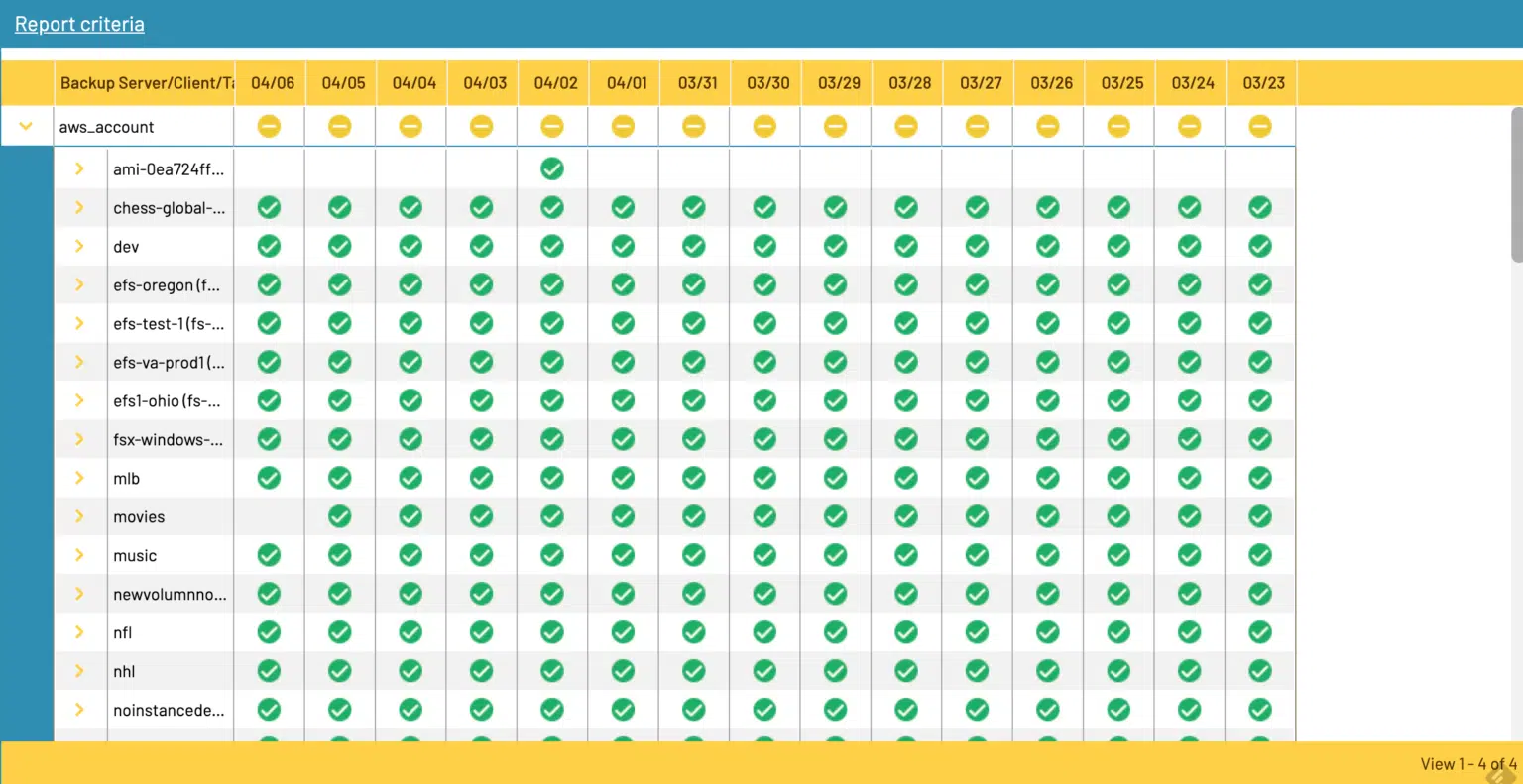
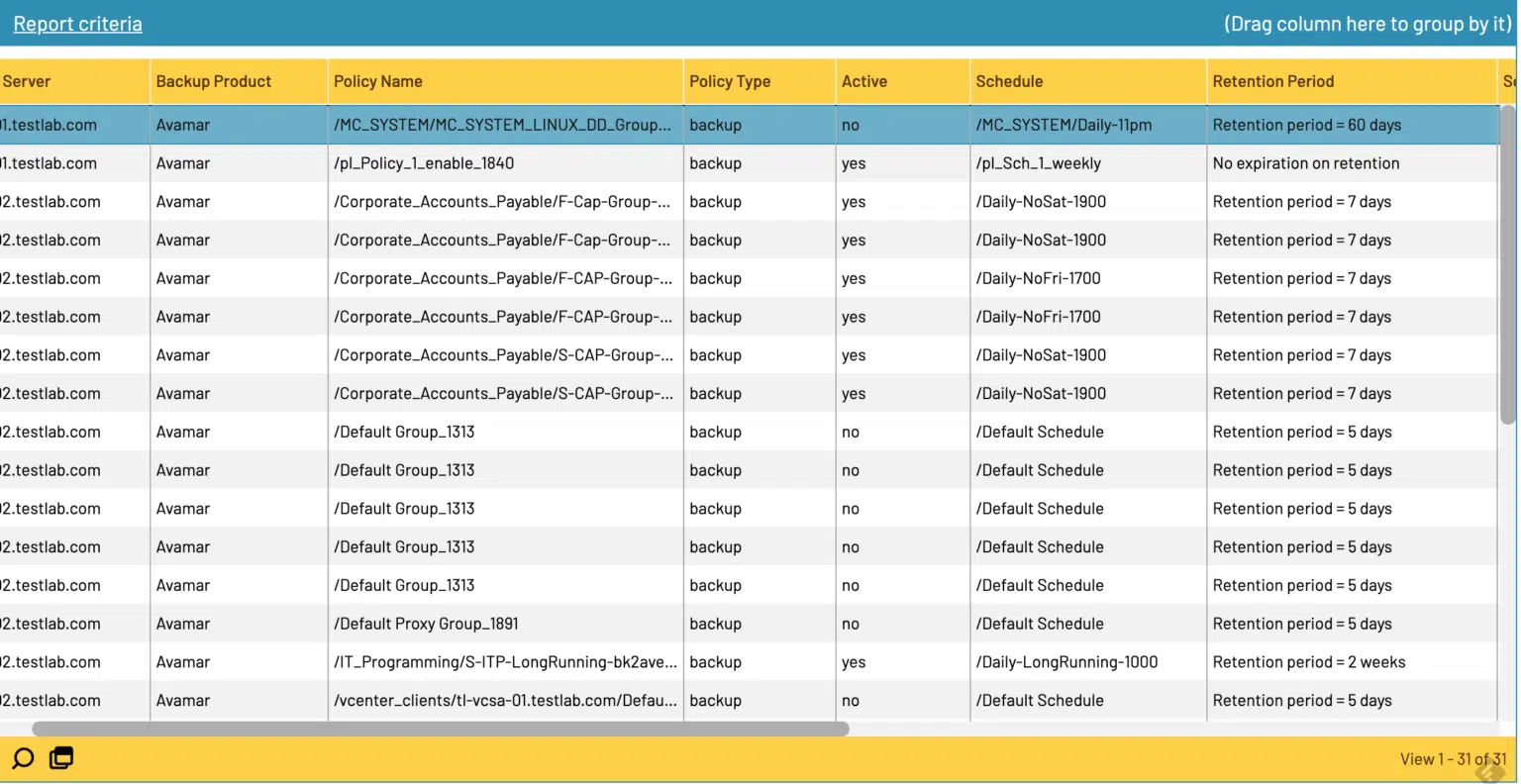
Any organization migrating to single or multi-cloud data protection environments should look for ways to efficiently review server or snapshot backup policy parameters across key metrics (e.g. schedule, backup type, retention rate). While this is taxing when done manually across a robust enterprise environment, automating policy configuration reporting offers several benefits. With just a few automated report runs on newly-created resources, you can gain confidence that policies are configured correctly. When done over time, you can enjoy quick reads that configurations continue to be accurate.
Here is a screenshot of Bocada’s automated cloud policy configuration reporting which allows for centralized visibility across cloud environments:
Ensure Cloud Resource Protection
Transitioning to cloud operations is a huge advantage when it comes to speed and ability to execute on IT projects faster than ever before. Yet that very speed of operations can also lead to key cloud resources being left unprotected and backup teams completely unaware of their presence.
By introducing automation to cloud asset protection, you’ll have an effective and efficient way to proactively identify unprotected AWS and Azure assets and add them to your backup policy schedule. For instance, in the Bocada AWS and Azure Asset Protection Reports detailed below, admins can enjoy a way to quickly identify unprotected assets and have a punch-list in-hand to address protection issues.
Overlay CMDB / Asset Inventory Validation
However, it’s not just AWS and Azure assets that need backup protection. What about all resources across your environment that should have cloud backup policies in place, including those that are currently on-prem? Without an effective way to tick and tie diverse resources to your cloud backups, you’ll be left unaware of critical resources being left unprotected.
With automated integration of your CMDB to your backup history, a key feature included in Bocada, you can remove these blinders entirely. Easily identify unprotected resources and create an action plan for addressing data protection holes.
Retain Legacy Backup Visibility
Even as you create a fully automated cloud data protection machine, it will likely be years before you can fully migrate away from legacy on-prem solutions. Date retention protocols, coupled with the time and resources needed to decommission legacy hardware and software, means managing cloud with on-prem backup infrastructure will likely be a juggling act for quite some time.
As a result, being able to sync performance data into a single dashboard, regardless of when or where that backup performance took place, will be an additional way to streamline operations and allow your team to evolve their know-how to the cloud while minimizing the need for training on legacy systems.
The Job Trends Report in Bocada does just that. By automating data collection across on-prem and multi-cloud systems, data protection administrators can streamline activities and centralize backup performance monitoring reporting.