In our recently released Backup Monitoring Trends Report, backup professionals cited incorporating backup monitoring into their cybersecurity programs as the #1 trend they expected to hit their category over the next 3-5 years.
This isn’t surprising. Consider the incredible range of organizations announcing ransomware attacks in just the past week: the parliament of Bosnia and Herzegovina, a New York City ambulance service, and telecom provider Bell Canada.
Everyone is a target. And the bigger the organization, the bigger the target.
This pressing problem calls for multi-layered approaches to cybersecurity planning. Consider introducing augmented, holistic backup operations monitoring as one such approach. Its proactive procedures give organizations a valuable tool to not just prevent cyberattacks but also be ready when they come.
Using Backup Monitoring To Go Beyond Data Restoration
Out of the gate, implement automated backup reporting. This means automating the aggregation of backup performance data from all backup solutions, normalize it, and put it under a single pane. Via one single console, you’ll immediately see if the assets in your environment are successfully backed up or not. It’s a key step in gaining a high-level view of backup restorability in the event of a cyber or ransomware attack.
This is critical. However, it’s just the very first line of defense.
It takes a point-in-time view of backup health without layering in additional proactive steps. It also assumes we have a strong handle on everything going on across the backup environment. As we’ll see below, that’s unlikely.
How To Use Backup Operations To Protect Against Cyber Criminals
This leads us to find ways to use backup operations as proactive cyber and ransomware protection tools. This means leveraging automated backup monitoring solutions to build stronger reads on backup environment health while also using them to identify unusual activity that could be a sign of cybercriminal activity.
Identify Critical Assets Without Any Safeguards
It’s one thing to be able to restore the assets you know are backed up. But what about assets that aren’t being backed up? If a ransomware or cyberattack hits when your environment has a good number of critical assets unprotected, you’ll still be left picking up the pieces.
Yet, this is a common scenario in many enterprise environments. When many teams have authority to create new assets, the backup team is rarely informed. This is especially the case in cloud and multi-cloud environments where IT responsibilities are further disbursed. The result is assets that need backup protection but are left vulnerable.
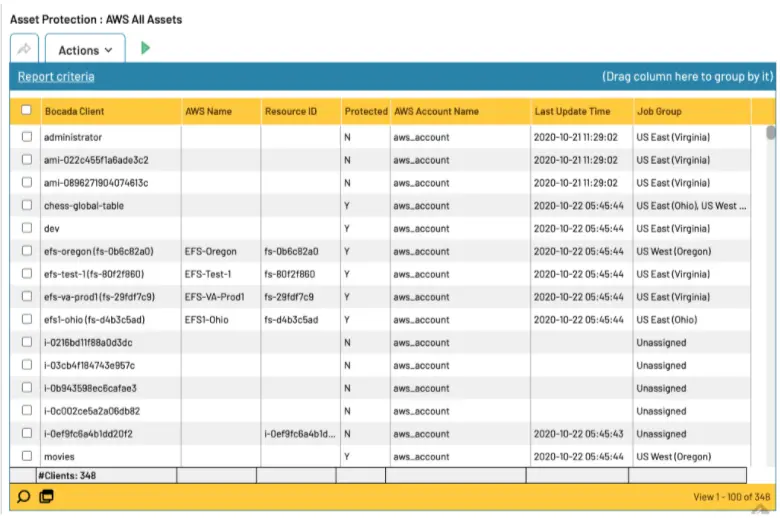
To counter this, implement a process of automated asset inventory reconciliation. By comparing the list of assets in asset inventory systems or CMDBs against backup job logs, you’ll quickly identify gaps. That is, you’ll pinpoint assets in your inventory with no active backup jobs. When you automate this process, no lag time exists. Your team can pull a list of unprotected assets weekly or monthly, and make unprotected asset oversight a regular activity.
Get Data Protection Holes Plugged Faster
Imagine losing critical data, or having to pay to get it back, because known problems did not get addresses quickly enough. This is a likely scenario when dealing with enterprise-scale ticket volumes. How do you prioritize which issues get addressed first, and ensure that they are quickly resolved? Through automated backup failure ticketing.
This process starts with programming what types of issues get priority tickets (e.g., failures on critical servers, jobs that failed multiple times), and triggering tickets when those issues occur. With this approach, you minimize ticket deluges so that team members can address hot-button problems. Further, this process also automates the porting of relevant failure information from backup systems into individual tickets, allowing team members to transition into failure fixing faster.
With faster, more targeted resolutions, critical data is backed up sooner and therefore restorable if necessary.
Spot Cybercriminal Activities Before They Become Big Issues
While the previous approaches proactively address data protection holes in the event of a cyberattack, they do not allow you to get ahead of it. And yet, holistic backup operations monitoring allows for this as well.
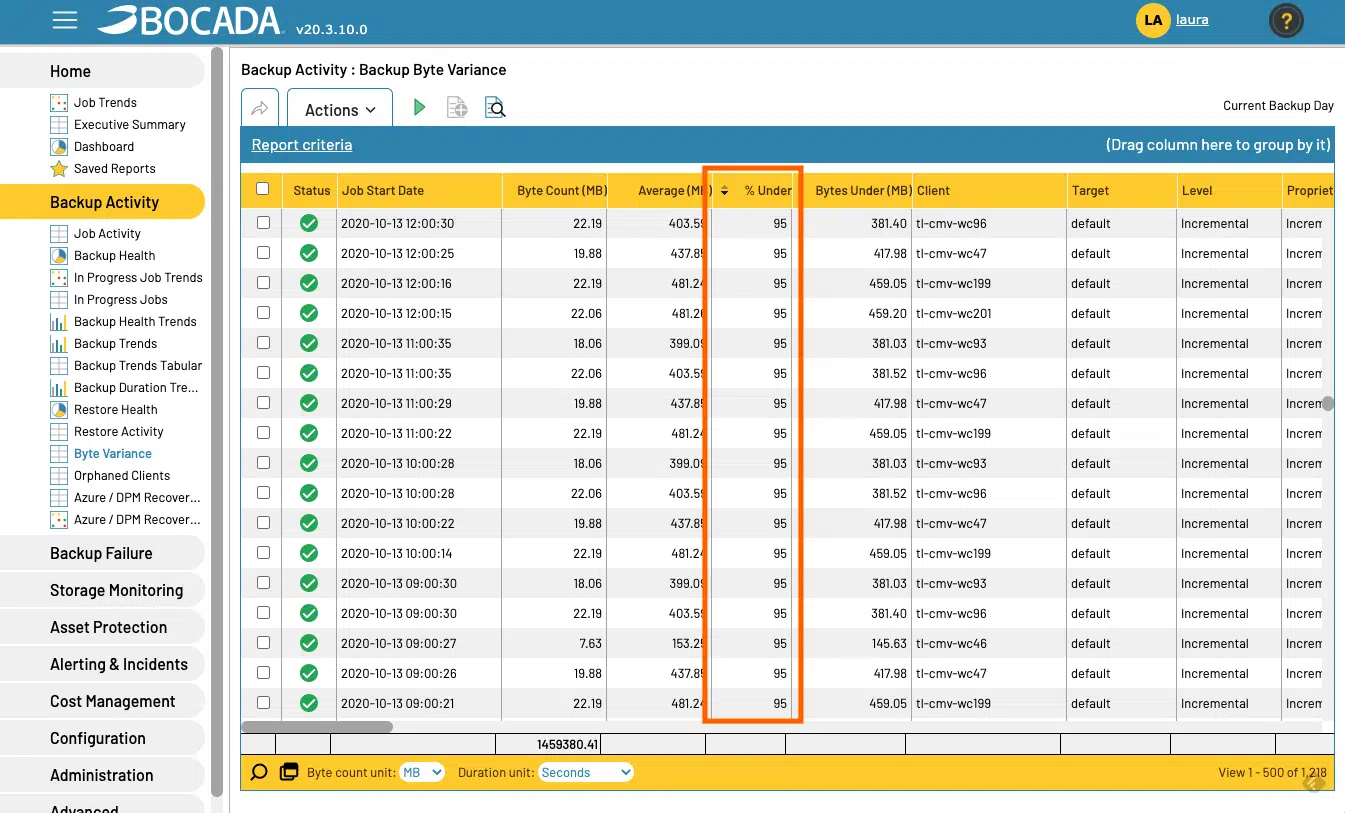
Consider backup byte volume. While data is growing at astronomical rates, the amount of data backed up over several days or even weeks is not that different. This makes pinpointing unusual variances in backup bytes so valuable.
Different types of ransomware attacks affect backup volume in unique ways. For instance, some ransomware completely removes files. This results in zero bytes backed up during the next backup job run. Other types of ransomwares change file names, copy the data over from the file, and then create a new file with the original name but remove all data from it. Once again, the amount of data backed up goes down dramatically.
In both scenarios, organizations could get ahead of these attacks with automated backup byte variance reporting or alerting. By understanding historical backup byte variance norms, automated backup monitoring systems can identify when backup activity does not meet expected patterns. While some data may be lost, variance reporting lets teams quickly identify issues and address them before they become newsworthy events.
Best Practices for Incorporating Backup Operations into Cybersecurity Plans
We’ve reached a stage where a cyberattack isn’t a matter of if, but when. Compounding this is that it often takes nearly 200 days to recognize that a cyberattack occurred. This means IT operations professionals must use a robust toolkit to stay one step ahead of cybercriminals.
As you consider weaving backup operations and improved backup monitoring into cybersecurity planning, keep the following best practices in mind:
- Consolidate On-Prem & Cloud Backup Monitoring Under A Single Pane: The first line of defense is streamlined backup monitoring to ensure that data is restorable. Look for solutions that natively integrate across your backup applications so that you can consolidate performance monitoring in one central view.
- Sync Asset Inventory Systems with Backup Logs: Find solutions that automatically reconcile asset inventories with backup log records and produce lists of assets with no backup history. This streamlines unprotected asset identification so you can quickly address data protection holes.
- Implement Automated, Trigger-Based Ticketing: Turn a hyper-manual process into a streamlined automated one with trigger-based ticket creation. Leverage solutions that allow you to customize ticket triggers and automate the creation and pre-population of tickets with failure information. Data protection teams will be able to address, and fix, issues faster.
- Leverage Unusual Activity Reporting: Leverage systems that automatically find patterns of backup behavior that deviate from historical norms. You’ll have a tool for unearthing issues before they become major events.
Solutions like Bocada include these capabilities out of the box, giving IT operations and data protection professionals a leg up on proactive cybersecurity protocols.
